Nmap Tracker
As an alternative to the router-based device tracking, it is possible to directly scan the network for devices by using Nmap. The IP addresses to scan can be specified in any format that Nmap understands, including the network-prefix notation (192.168.1.1/24) and the range notation (192.168.1.1-255).
Please keep in mind that modern smart phones will usually turn off WiFi when they are idle. Simple trackers like this may not be reliable on their own.
Configuration
To add the Nmap Tracker integration to your Home Assistant instance, use this My button:
If the above My button doesn’t work, you can also perform the following steps manually:
-
Browse to your Home Assistant instance.
-
In the bottom right corner, select the
Add Integration button. -
From the list, select Nmap Tracker.
-
Follow the instructions on screen to complete the setup.
An example of how the Nmap scanner can be customized:
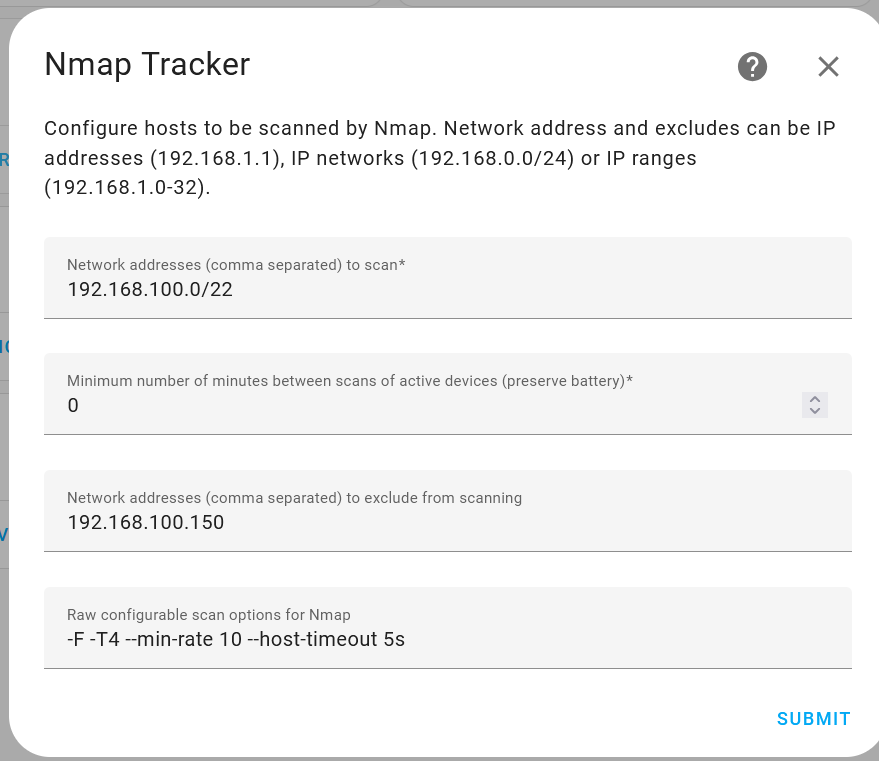
Network range to scan using CIDR notation. In the example above it will scan addresses from 192.168.100.0 to 192.168.103.255.
Frequency of the scans. The lower the number, the quicker it will detect devices connected and disconnected usually at the cost of the devices battery life. The example above will scan every minute.
A comma-separated list of IP addresses not to scan. The above example will skip 192.168.100.150.
Nmap command line parameters which can be used to configure how Nmap scans the network. For more details see Nmap reference guide.
See the device tracker integration page for instructions how to configure the people to be tracked.